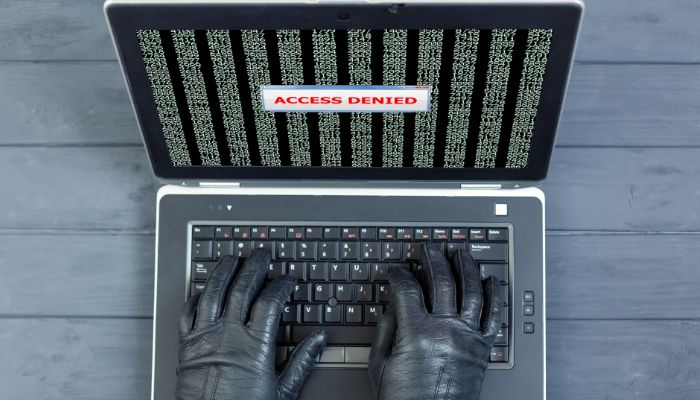
Understanding Brute Force Attacks: How Cybercriminals Crack the Code
In the ever-evolving cybersecurity landscape, one term that often sends shivers down the spine of security professionals and individuals alike is “brute force attack.” It’s a method employed by cybercriminals to gain unauthorized access to systems, accounts, or encrypted data. In this blog, we will delve deep into the world of brute force attacks, exploring what they are, how they work, and, most importantly, how you can protect yourself or your organization from falling victim to them.